Zunami Protocol - REKT
NOTE: This article has been edited to remove reference to Ackee Blockchain, who audited an earlier version of the protocol before the attacked MimCurveStakeDAO strategy was added.
The Curve ecosystem can't catch a break…
Yesterday, Zunami Protocol lost $2.1M as the project’s Ether- and USD-pegged stablecoins came under a price manipulation attack.
Although Curve itself was unaffected, the exploiter drained Zunami’s zETH and UZD liquidity pools on Curve, causing the ‘zStables’ to depeg by 85% and 99%, respectively.
Peckshield raised the alarm but, after the recent BlockSec/Curve debacle, was careful not to provoke criticism and opted not to provide transaction hashes or addresses.
Shortly after, Zunami confirmed the exploit:
It appears that zStables have encountered an attack. The collateral remain secure, we delve into the ongoing investigation.
First Conic Finance, then JPEG’D, Alchemix and Curve itself, now Zunami…
Could the Curve Wars be proving even more lucrative for hackers than for protocols?

Credit: Peckshield, BlockSec
Just over an hour after the initial alert, and presumably after confirming no further funds were at risk, Peckshield followed up with more detail:
It is a price manipulation issue, which can be exploited by donation to incorrectly calculate the price as shown in the following figures.
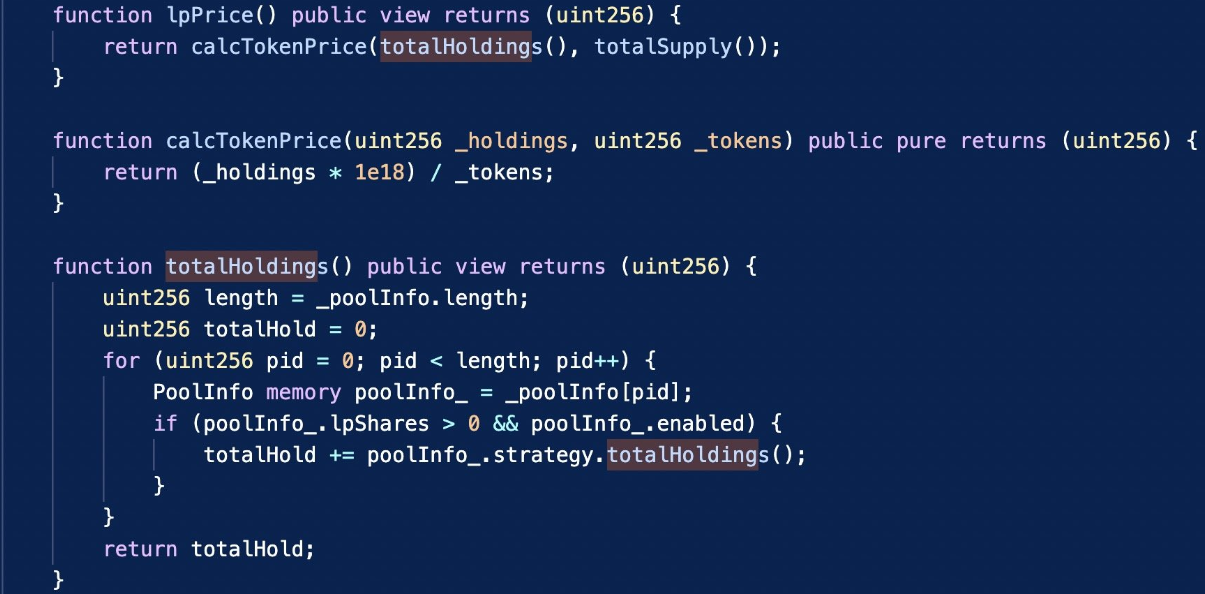
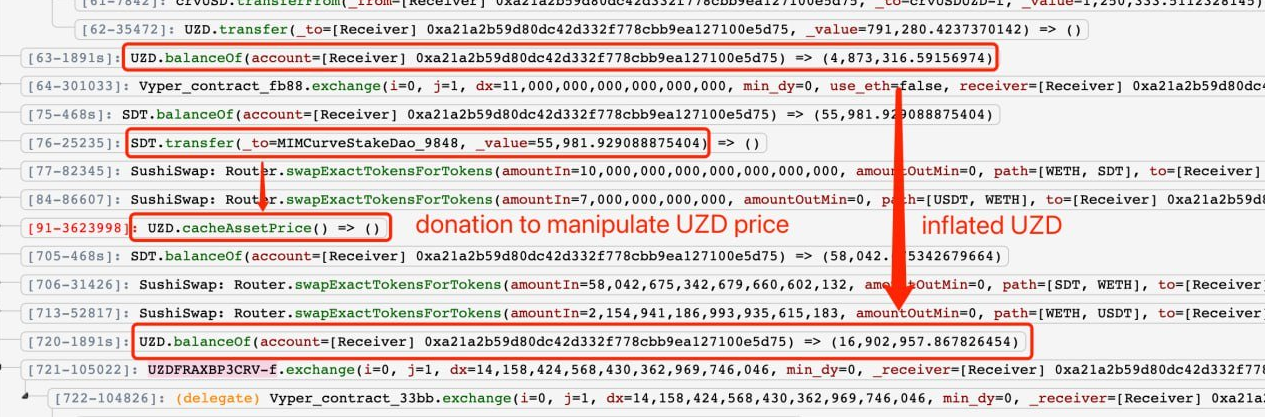
The attacker used flash loans to execute large token swaps (e.g. SDT), causing slippage in the pool which could be used to manipulate LP token prices. The root cause was a flawed price calculation via the totalHoldings function.
BlockSec provided the following step-by-step:
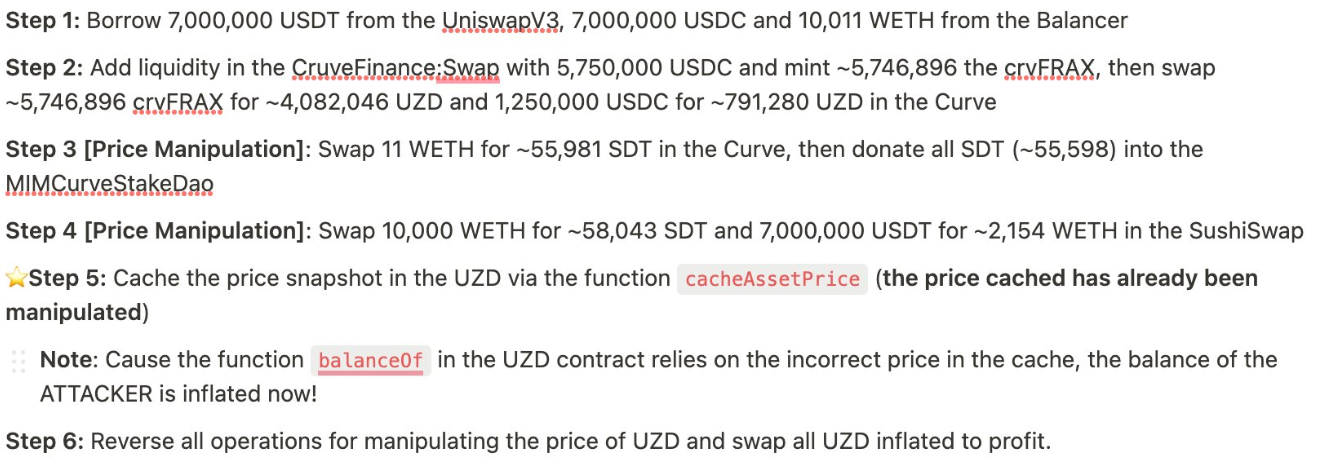
The proceeds (1184 ETH or $2.1M) were quickly deposited into Tornado Cash.
The protocol itself and the UZD and zETH contracts were audited by Hashex.
Attacker’s address: 0x5f4c21c9bb73c8b4a296cc256c0cde324db146df
Exploit tx (zETH): 0x2aec4fdb…
Exploit tx (UZD): 0x0788ba22…
The Sushiswap SDT pool, although used by the hacker during the price manipulation, is safe (despite what a certain relentless bear-poster might like to imply).

Peckshield may have been careful not to include sensitive information in their alert, but others weren’t so cautious.
Following BlockSec’s public announcement of the root cause behind the Vyper bug last month, the backlash prompted a debate about how many security firms apparently chase Twitter clout while potentially aiding hackers.
The discussion, and calls for feedback, appear to have led to tweaked alerting standards which prioritise only the crucial information to alert users who may need to withdraw funds, but without giving away any clues which bad actors may take advantage of.
Another step forwarded is the SEAL 911 hack hotline; the Telegram bot aims to use its list of members is a fast-response for any concerned whitehat looking to alert a potentially vulnerable protocol’s team.
Security teams do important work in DeFi, where exploiters are lurking around every corner.
Not least BlockSec, with their impressive whitehacking record.
But keeping DeFi safe is a constant game of cat-and-mouse, one that can’t always be won.
Who will be next to fall prey?

REKT作为匿名作者的公共平台,我们对REKT上托管的观点或内容不承担任何责任。
捐赠 (ETH / ERC20): 0x3C5c2F4bCeC51a36494682f91Dbc6cA7c63B514C
声明:
REKT对我们网站上发布的或与我们的服务相关的任何内容不承担任何责任,无论是由我们网站的匿名作者,还是由 REKT发布或引起的。虽然我们为匿名作者的行为和发文设置规则,我们不控制也不对匿名作者在我们的网站或服务上发布、传输或分享的内容负责,也不对您在我们的网站或服务上可能遇到的任何冒犯性、不适当、淫秽、非法或其他令人反感的内容负责。REKT不对我们网站或服务的任何用户的线上或线下行为负责。
您可能也喜欢...
Zunami Protocol - Rekt II
$500k vanished from Zunami Protocol in a mid-May admin key exploit. Months of stagnant development & perfect timing may have paved the way. Team offered weak excuses, dismissed concerns, left users empty-handed. When emergency keys open doors, who's in control?
Tapioca DAO - Rekt
Another day, another private key theft, another protocol rekt. Tapioca DAO on Arbitrum suffers a roughly $4.4 million loss in a private key compromise. Some funds have been recovered, though the full extent of the damage remains to be seen.
Radiant Capital - Rekt II
Radiant Capital gets a $53M haircut. Thought multi-sigs were safe? Think again. Radiant's "robust" 3/11 setup crumbled like a house of cards. Exploited twice in 2024, the future of Radiant looks about as bright as a black hole.
