Is Age Verification a Trap?
Imagine having to show your ID to read a newspaper.
Not to buy it, not to subscribe. Just to read it - standing at the corner, or sitting at your kitchen table, or checking what your government did while you slept. Present your identity first, then you may proceed.
That used to sound like the kind of thing that happened somewhere else. Now it is the stated policy goal of the United States, the United Kingdom, the European Union, and a growing list of governments that have decided the internet needs a front desk.
They call it age verification. They say it is for the children. Every bill in this wave invokes children. The titles change. The justification never does.
But the infrastructure being built has nothing to do with children and everything to do with identity - who you are, where you go, what you read, and whether someone with the right clearance can find out.
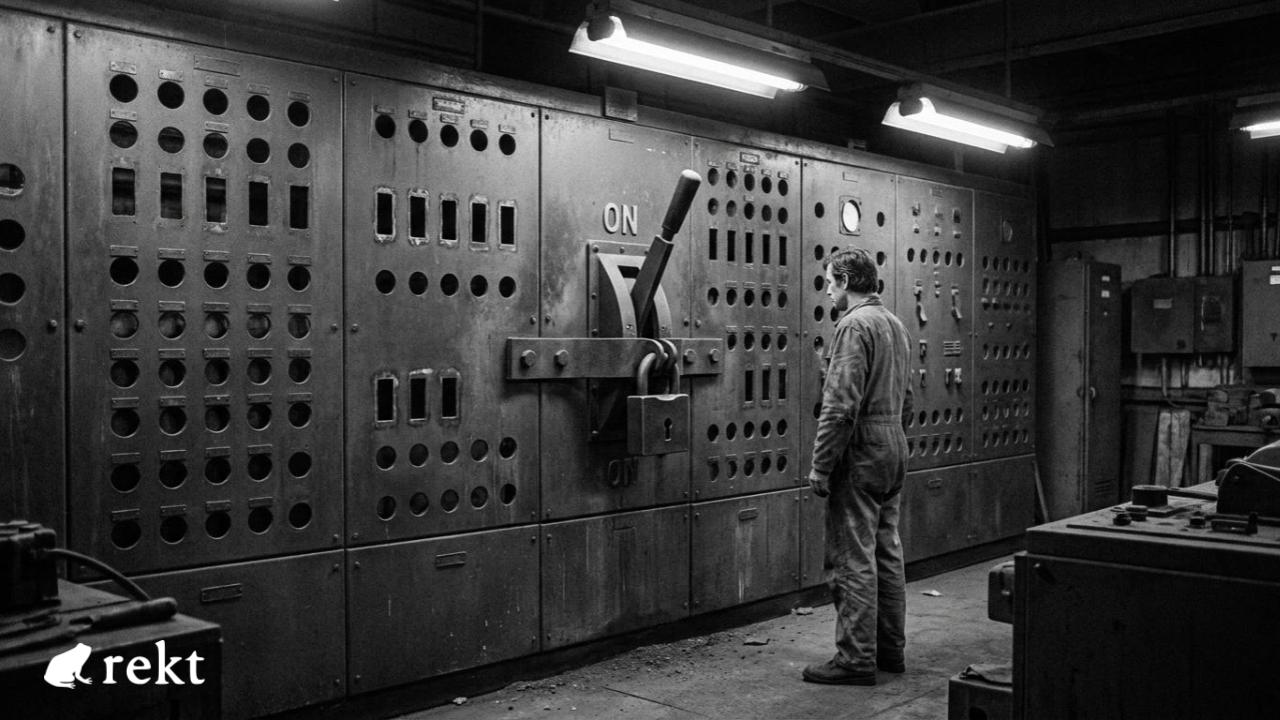
The age gate is the Trojan horse. Inside it is something that has no off switch, no sunset clause, and no mechanism for the public to vote it back out.
Once you build a database of verified identities tied to internet behavior, you have built a surveillance apparatus.
The question of who controls it, and under what laws, comes later, under different leaders, with different priorities, and without your consent.
The system is already being assembled. Some of it is already live.
So before you decide whether you trust the people building it, did anyone actually ask you if you wanted it built?

Dr. Corey Petty has spent his career inside the systems most people never see.
His day job is evangelizing Logos at the Institute of Free Technology, a technology stack aimed at digital sovereignty.
The phrase he uses to tie the whole thing together: "Building asshole-resistant technology."
Technology worth building, in his view, is technology that holds up under pressure and doesn't punish the people it's supposed to serve.
A conversation with him about age verification informed some of what follows.
His read on the enterprise is worth stating upfront: "It is theater."
Before an age gate ever loads, before you click agree, before you hand over a single document - your browser has already talked.
Open the Logos article “Your Browser Has Already Betrayed You”, written by Dr. Corey Petty, and the page demonstrates it to you in real time.
Your hardware. Your screen dimensions. Your graphics card. Your timezone. Your location. Broadcast the moment the page loaded, without a prompt, without your knowledge.
No age gate required. No law required. The surveillance infrastructure already exists. Age verification doesn't create it. It dresses it in a suit and gives it a legal address.
On April 14, 2026, the European Union launched its flagship digital identity app, the centerpiece of a continent-wide age verification mandate years in the making.
Security consultant Paul Moore sat down with it on launch day. He was done in under two minutes.
He removed the PIN encryption values from the app's shared preferences file, restarted the app, and picked a new PIN.
The app handed over the original user's verified identity credentials without complaint, without an alert, without logging anything had changed.
The architecture that failed wasn't incidental. The PIN was not cryptographically tied to the identity data it was supposed to protect.
Rate limiting was an incrementing number in the same config file, reset it to zero and you can keep guessing indefinitely.
The biometric check was a single boolean value. Set it to false and the app skips that step entirely.
Three separate security mechanisms. One file. One edit undoes all of them.
Either the people who built it are catastrophically incompetent, or protecting the user was never the primary design goal.
"It is theater" as the conversation with Petty put it.
The appearance of security, erected so governments can point at something, legislators can vote for something, and parents can feel that something has been done.
The EU app is the visible failure. Underneath it is what actually matters.
Persona, one of the leading identity verification vendors in the United States, had 53 megabytes of its source code exposed earlier this year, not stolen through a breach, simply visible on a FedRAMP-authorized server.
What it revealed was not a tool built to check whether someone is old enough to watch a video.
It was a surveillance platform with 269 surveillance checks per user, facial recognition against watchlists, SAR filing capability to FinCEN, the Treasury's financial intelligence unit, and biometric retention for up to three years.
Persona CEO Rick Song stated: "We do not work with any federal agency today. We do not want our technology to be used by ICE or the government for any surveillance purposes."
That denial sits on the record.
The switch not being flipped today, however, is not the same as the switch not existing.
In October 2025, Discord lost 70,000 government-issued ID images through a third-party vendor.
A dating app leaked 72,000 selfies a few months beforehand.
These are not hypotheticals. They are the documented pattern of what happens when centralized identity repositories meet the lowest bidder in the vendor chain.
You can change your password. You cannot change your face.
Hans Christian Andersen's emperor paraded through the streets in clothes that didn't exist, and every minister, every courtier, every citizen along the route saw nothing and said nothing, because saying nothing was safer than being the one who pointed.
The EU launched an age verification app that a security researcher defeated in the time it takes to make a cup of coffee, and the mandate continued, the rollout continued, and the political speeches about protecting children continued, because the alternative was admitting that what was built was not what was promised.
It took a child to say the emperor had no clothes. It took Paul Moore two minutes to say the app had no security.
If the system can't protect your identity from a text file edit, what exactly is it protecting, and for whom?
The Ratchet
No jurisdiction that has passed age verification legislation has ever repealed it. Not one. That is not a coincidence. It is the mechanism.
In the United States, Louisiana moved first, in 2022, requiring age verification for adult content websites. It looked like a narrow, defensible policy aimed at a specific category of harm.
By the end of 2025, half the country had passed a law requiring age verification to access adult content or social media. Nine states passed new laws in 2025 alone.
By overdoing it and calling it the law, you give legislators something to point to. Technology creates the standard. Then the standard becomes permanent.
The ratchet is not a metaphor borrowed from machinery. It is the observable legislative pattern, documented in real time, in real jurisdictions, turning in one direction with no reverse gear built in.
On April 1, 2026, Apple shipped iOS 26.4 to their UK users. The update added age verification at the device level, tied to Apple ID, affecting downloads, settings, and app usage system-wide.
Those who decline to verify are not locked out. They are placed into something quieter: Web Content Filter blocking access across Safari and every third-party browser, Communication Safety scanning your images and messages for nudity.
Non-compliance does not result in exclusion. Apple will treat your account like it belongs to a minor.
Proton documented that UK law does not require this specific implementation. Apple attributed it to the law anyway.
That is the ratchet: Go further than required, name the law as cover, and the expanded version becomes the floor for whatever comes next.
Big Brother Watch noted that one in three UK adults has no credit card and one in five holds no driving license, the only two forms of ID Apple accepts.
This is higher among disabled people, women, low income groups and younger adults, especially in urban areas.
The default for those who cannot comply is a child-locked device. The least documented inherit the most restrictive outcome, by design.
Now the ratchet is turning on the last tool people use to step around it.
When Florida's age verification law took effect, VPN usage spiked 1,150 percent in the first 4 hours.
Governments took note, and not in the way you would hope.
Wisconsin proposed a VPN ban - then scrapped it after public backlash, only for the governor to veto the broader bill entirely.
Michigan proposed banning VPN distribution outright.
Utah Senate Bill 73, effective May 6, 2026, makes Utah the first US state to hold websites legally liable even when a user bypasses the requirement through a VPN.
Across the Atlantic, the EU's Executive Vice-President Henna Virkkunen signaled in March 2026 that Brussels may need to address VPNs being used to bypass age verification systems.
France's Digital Affairs Minister Anne Le Hénanff was less measured. VPNs, she said, are "next on my list."
Nym, which builds privacy infrastructure, read the direction of travel plainly: Age verification is a backdoor VPN ban.
The stated goal is protecting children. The functional outcome is eliminating the last widely accessible method of anonymous internet use.
Then there is the Parents Decide Act, HR 8250, introduced in the US Congress on April 13, 2026.
It would require every US operating system to collect date of birth at device setup and make that data accessible to every app installed on the device.
Implementation is delegated entirely to the FTC within 180 days of passage.
The hard questions, what counts as verification, what data can be retained, what government access is permitted, are left for unelected appointees to answer after the framework is already law.
The Real ID set the same pattern - open-ended authority, at the discretion of the agency head.
The terms get filled in later, by whoever is running the agency, under whatever political conditions exist at that moment.
Then, on April 30, 2026, the Senate Judiciary Committee voted 22-0 to advance the GUARD Act, sponsored by Senator Josh Hawley of Missouri.
The bill would require AI chatbot companies to verify the age of every American who wants to use them.
Hawley celebrated on Twitter: "My bill to stop AI from telling kids to kill themselves just passed out of committee UNANIMOUSLY. No amount of profit justifies the DESTRUCTION of our children."
Read the bill's text, and a different picture emerges.
A "reasonable age verification measure," under the GUARD Act, cannot mean asking users to confirm they are not a minor or to enter their own birth date
What it can be is a government ID upload, a facial scan, or a financial record tied to your legal name.
Not for children. For every American who wants to ask a chatbot for help with their taxes, their homework, their billing dispute, or anything else.
The EFF says that definition reaches well beyond companion apps - service bots, search assistants, homework helpers, the general-purpose tools millions of adults use every day.
A teenager asking for algebra help would need to clear the gate. So would the adult sitting next to them.
Trade group NetChoice called it plainly before the vote: Forcing AI companies to collect and store highly sensitive personal documents creates honeypots for cybercriminals to exploit.
The committee voted unanimously anyway.
Senators Richard Blumenthal and Chris Murphy signed on as Democratic co-sponsors.
The bill now heads to the Senate floor with bipartisan momentum that age verification proposals rarely carry.
The infrastructure will not check whether a user is a child before it asks for their ID. It will ask everyone.
From adult websites in Louisiana in 2022, to every AI interaction in the United States in 2026. A slow push for four years, now gaining momentum.
Every step is justified by the last. Every expansion presented as a reasonable extension of something already agreed to.
The ratchet does not announce itself. It just turns.
When they've closed every exit and called it safety - what legal argument do you have left, and who exactly decides whether your consent was voluntary?
The Consent Fiction
The Supreme Court took up Chatrie v. United States on April 27, 2026.
The government's position: Chatrie opted into Google Location History, surrendering any privacy expectation in that data. He chose to use the service. Whatever Google collected, he handed it over voluntarily.
Chief Justice Roberts extended the logic from the bench: "If you don't want them to peer into your window, you can close your window, or the shades."
Justice Gorsuch said the government's argument, if accepted, would mean that it would not need a warrant to surveil who is at a church or a political rally, whether or not a crime took place.
Justice Sotomayor put the question directly to the government: "There are certainly Google documents that show that it's very hard and if not opaque to figure out how to turn these things off, correct?"
How voluntary is consent that's designed to be invisible?
Analysts who read the oral arguments expect the court to allow geofence warrants under certain conditions, enough to keep the door open for everything that follows.
A ruling is expected by the end of June 2026. If it lands that way, the voluntary exposure doctrine becomes further entrenched, and every age verification database on the planet inherits the same legal logic.
You chose to use the internet. You chose to click agree. Whatever was collected, you handed over.
The Fourth Amendment, the protection against unreasonable government search, stops at the terms of service you didn't read.
The surveillance didn't begin with Chatrie. It began the moment you arrived. Before any law required it, before any gate existed, your browser was already talking.
Open the Logos article and it shows you in real time: Your hardware, location, screen dimensions, timezone, all of it broadcast the instant you arrived, without a prompt, without a choice.
The age gate does not start the surveillance. It converts pre-existing passive data collection into an active, named, government-accessible identity infrastructure.
Before the database, the data sat in fragments across servers you'll never see.
After it, your face is attached to your behavior, and accessing it requires nothing more than a warrant or the right political moment.
The trap is being set.
Representative Chip Roy of Texas said it from the floor of the House during a FISA debate with a directness that does not require editorial framing: "This body ought to be defending the people of the United States against the power of government being used against us. Under no circumstances should we allow technology to breach the wall that the Fourth Amendment created."
Roy is a Republican from Texas. This is not a partisan argument. The wall he is describing is the one the voluntary exposure doctrine is being built to dismantle, with the Supreme Court's apparent blessing, while legislators name new bills after children and call it safety.
Each framework installs the mechanism first and fills in the rules later - the Real ID Act, the Parents Decide Act, the GENIUS Act's freeze-and-seize capability for stablecoins, the GUARD Act's identity verification regime for every AI interaction in the country - All written the same way: Infrastructure locks in, oversight comes after, without another vote, without further consent.
You consented when you clicked agree. That is the argument. That is the whole argument. And it is being prepared as the permanent legal answer to every objection that follows.
When consent is buried in settings the company describes as opaque, and the court is poised to call it voluntary, at what point does agreeing to use the internet become agreeing to everything the internet is allowed to do to you?
The Endgame
Peter Thiel's Founders Fund led Persona's $150 million Series C and $200 million Series D funding rounds.
Thiel co-founded Palantir, which has been a core contractor for US Immigration and Customs Enforcement for over a decade, building the surveillance infrastructure used to track, identify, and deport immigrants.
Persona's CEO has stated clearly that there are no DHS or ICE partnerships and no federal agency relationships.
That denial is on the record. So is the investment chain. Confirmed facts do not require inference to be worth knowing.
The investment chain is not evidence of what Persona does today. It is evidence of who finds the capability worth owning, before the rules about how it can be used are written, by appointees, without another vote.
The internet was not built as a surveillance apparatus.
It scaled, and became the connective tissue of modern life, and then someone decided the data flowing through it was worth more than the people generating it.
The decision was not announced. It was implemented in defaults nobody changed and terms nobody read.
Age verification is building the same pattern with identity data.
The decision about what to do with it comes later.
As the conversation with Petty put it: "Give data under centralized control, eventually someone else takes charge."
Not the people who passed the law. Someone else, under different priorities, with the legal authority to act because the framework is already running.
De-identification is the word the industry uses to suggest that data stripped of your name is no longer about you.
It has not been true for years. Researchers have found that over 99% of Americans could be correctly re-identified in any dataset using just 15 demographic attributes.
Your age, your device, your location at verification time, your browsing pattern around the gate - the profile assembles itself.
The name is the last thing they need. The moment you add de-identification, they have a profile. There is no undo button.
Speed is not a bug in this process. It is a feature. Get the infrastructure running before the objections can be organized. Get the data flowing before the courts rule on whether it should.
The EU wallet certification happened before the app could survive two minutes with a security researcher.
The Parents Decide Act delegates everything to the FTC.
As Dr. Petty put it: "The fast path to deployment is the faster way to gain control."
This is not a prediction. It is a description of documented events that predate every law discussed in this piece.
T. Candice Smith's car locked up at seventy miles an hour on Interstate 15 because a payment was late.
Santoshi Kumari's ration card was cancelled because her fingerprints failed biometric authentication, and she died asking for rice.
Journalist Liu Hu was blacklisted in China and discovered he could no longer buy a plane ticket, use a high-speed train, purchase property, or take out a loan. "There was no file, no police warrant, no official advance notification. They just cut me off from the things I was once entitled to."
The World Economic Forum praised China's digital currency system as a model that "democratizes access to banking services."
These are not cautionary tales. They are the pattern. The infrastructure being debated today already has a body count, as highlighted in our piece from December 2025 - The Economy of Access.
The apparatus of control does not advertise itself as the apparatus of control. It advertises itself as progress.
Once it is out you cannot put it back in the box. Central databases are not neutral infrastructure.
They are weapons, in the sense that any tool with the capacity to include has the capacity to exclude, and any system that can verify identity can deny it.
The question of who holds that power, and under what conditions they exercise it, is the only question that matters.
It is also the question that gets answered last, after the ratchet has turned far enough that reversing it would require dismantling something governments, platforms, and vendors have spent billions building.
Some legislators are pushing back in the US. On April 23, 2026, Representatives Thomas Massie and Lauren Boebert introduced the Surveillance Accountability Act - H.R. 8470 - which would require the government to obtain a warrant before accessing your data, location, biometrics, or any information held by a third party.
It closes the third-party doctrine loophole the government has used for decades to bypass the Fourth Amendment.
The bill was filed before Speaker Johnson unveiled a three-year FISA extension with zero warrant requirements.
Congress couldn't agree on reforms, so it passed a 45-day stopgap instead, no warrant requirement, no meaningful change, and kicked the fight to June.
So the question is not whether anyone is fighting. The question is whether a bill in committee is enough to stop an infrastructure already running at scale.
A Digital Privacy Bill of Rights would go further - not a warrant requirement for what the government can access after the fact, but a declaration that identity is not a toll in the first place.
That reading is not a transaction. That the internet belongs to the people who use it, not the infrastructure built around them.
During the conversation with Dr. Petty, he dropped some inspiration: "Change comes from people getting together and solving problems. Technology should conform to people's needs, not the other way around."
The EFF has documented every step of the ratchet.
Big Brother Watch called it a serious and unprecedented step that risks undermining privacy, freedom of expression, and equal access to information, and wrote to Apple demanding they drop the ID check.
Proton's CEO said age verification as currently proposed would mean the death of anonymity online.
These are not fringe voices. They are the child in the crowd who has looked at the emperor and said what everyone else is pretending not to see.
The infrastructure is being assembled in plain sight. The mandate is expanding in documented increments. The legal framework to protect it from constitutional challenge is being settled by the Supreme Court as you read this. The legislation is named after children so that questioning it requires you to first explain that you are not against children.
The apparatus of control does not ask permission. It asks for your face, your age, your ID - and once it has them, the things you value, the things that run your life, can be pulled from underneath you without a file, without a warrant, without advance notice.
Once it is out, you cannot put it back in the box.
When the box is sealed, will you remember you had the chance to stop it?

The day the internet requires identification will be announced with great fanfare.
There will be a bill signing. Somebody will invoke the children. Senators and Congress critters will run victory laps.
The infrastructure will already be running. It will have been running for years - in the verification vendor's server, in the device-level age check, in the terms of service you clicked through without reading.
This is how it always goes. Real ID was signed into law in 2005. It took twenty years and a dozen deadline extensions to fully implement, and it landed anyway.
Net neutrality was written, repealed, rewritten, repealed again, and the internet changed anyway.
Every time the legislative fight stalled, the agenda migrated somewhere harder to stop.
Into default settings. Into platform policy. In terms of service nobody reads. If the law won't carry it, the user agreement will.
That is the final delivery mechanism. The one that bypasses every vote, every court, every amendment, and arrives as a notification on your phone one Tuesday morning
The announcement is the last step, not the first. By the time it is made, the decision will already be done.
You will click agree. You will not notice. And the version of the internet where you could read, search, question, and dissent without first proving who you are will be gone so quietly that most people will not remember it existed.
That is how the trap works. Not with a lock and a key. With a series of reasonable-sounding steps, each one justified by the last, until the door you came in through is no longer there.
The systems are insecure by design. The mandate expands by ratchet. The legal framework to protect it from challenge is being assembled by the Supreme Court.
The legislation is bulletproofed with children's names.
And the people who find the capability most valuable are already closest to it, waiting for the rules to be written in their favor, by appointees, without another vote.
You have seen all of this. The question is whether seeing it is enough.
A Digital Privacy Bill of Rights does not exist yet.
This is a call to build one - not a technical document, but a political declaration.
That identity is not a toll. That reading is not a transaction. That the internet belongs to the people who use it, not the infrastructure erected around them.
The surveillance apparatus exists because people decided to build it.
A Digital Privacy Bill of Rights should exist for the same reason, if enough people decide it should.
Every system in this piece was built by someone who decided to. That decision belongs to you too.
The emperor has no clothes. The app has no security. The gate is not for the children.
They didn't ask you if you wanted this built. Are you going to let them finish without a fight?

REKT作为匿名作者的公共平台,我们对REKT上托管的观点或内容不承担任何责任。
捐赠 (ETH / ERC20): 0x3C5c2F4bCeC51a36494682f91Dbc6cA7c63B514C
声明:
REKT对我们网站上发布的或与我们的服务相关的任何内容不承担任何责任,无论是由我们网站的匿名作者,还是由 REKT发布或引起的。虽然我们为匿名作者的行为和发文设置规则,我们不控制也不对匿名作者在我们的网站或服务上发布、传输或分享的内容负责,也不对您在我们的网站或服务上可能遇到的任何冒犯性、不适当、淫秽、非法或其他令人反感的内容负责。REKT不对我们网站或服务的任何用户的线上或线下行为负责。
