Moola Market - REKT
Lending protocol Moola Market is the latest to fall victim to a “highly profitable trading strategy”, and the first CELO protocol on the rekt.news leaderboard (#63).
Similarly to last week’s Mango Markets case, the exploit was carried out via price manipulation of a collateral asset, this time netting the attacker $8.4M.
The Moola team announced the incident on Twitter, appealing to the CEX-funded attacker to return funds in exchange for a bounty.
Fortunately, just six hours later, over 90% of the funds were returned to the Moola multisig, with the exploiter keeping ~$525k as a bounty, of which $37k was donated to charity…
A guilty conscience or a planned whitehat?

Credit: FrankResearcher
This attack was a simple price manipulation which didn’t require any coding.
Using initial funding of 243k CELO (~$180k), the attacker supplied 60k CELO in order to borrow 1.8M of the protocol’s native token, MOO, which could itself be used as collateral to borrow against other assets.
Then, using the remaining CELO to buy MOO on Ubeswap, the attacker pumped the price of their MOO collateral…
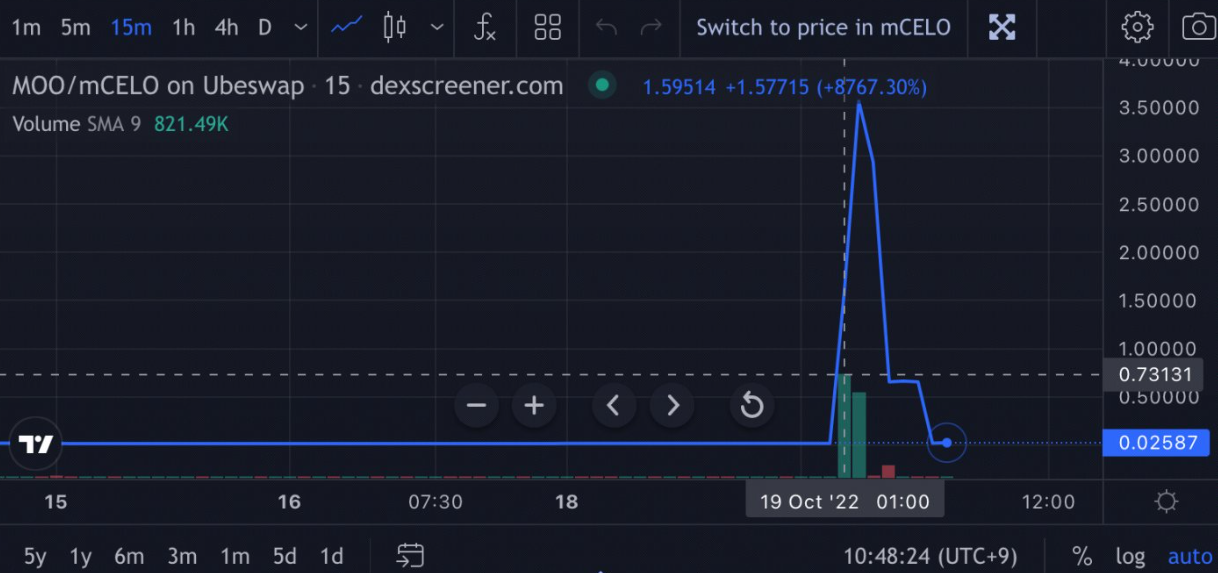
…allowing them to borrow the remaining assets on the protocol, draining all liquidity:
- 8.8M CELO ($6.5M)
- 765k cEUR ($0.7M)
- 1.8M MOO ($0.6M)
- 644k cUSD ($0.6M)
Attacker's address: 0x95b5579b323ddc6cd290bd4da6e56ba019588efc

In addition to returning the majority of the funds, the whitehat also donated 50k CELO ($37k) of the bounty to Impact Market, a protocol focused on providing UBI for vulnerable families in developing countries.
Bear markets offer easy opportunities to market manipulators, who find it easier to move prices when liquidity is low. Especially when smaller protocols allow use of their native tokens as collateral, whose dollar value dies away as the bear drags on.
Moola Markets have learned their lesson, and are proposing to remove MOO as a viable collateral asset via protocol governance.
But anyone with deep enough pockets can stress test DeFi markets in their current state.

REKT serves as a public platform for anonymous authors, we take no responsibility for the views or content hosted on REKT.
donate (ETH / ERC20): 0x3C5c2F4bCeC51a36494682f91Dbc6cA7c63B514C
disclaimer:
REKT is not responsible or liable in any manner for any Content posted on our Website or in connection with our Services, whether posted or caused by ANON Author of our Website, or by REKT. Although we provide rules for Anon Author conduct and postings, we do not control and are not responsible for what Anon Author post, transmit or share on our Website or Services, and are not responsible for any offensive, inappropriate, obscene, unlawful or otherwise objectionable content you may encounter on our Website or Services. REKT is not responsible for the conduct, whether online or offline, of any user of our Website or Services.
you might also like...
Tapioca DAO - Rekt
Another day, another private key theft, another protocol rekt. Tapioca DAO on Arbitrum suffers a roughly $4.4 million loss in a private key compromise. Some funds have been recovered, though the full extent of the damage remains to be seen.
Radiant Capital - Rekt II
Radiant Capital gets a $53M haircut. Thought multi-sigs were safe? Think again. Radiant's "robust" 3/11 setup crumbled like a house of cards. Exploited twice in 2024, the future of Radiant looks about as bright as a black hole.
Surviving Digital Danger
Think you've mastered the crypto minefield? Think again. Surviving Digital Danger - The rekt guide to turning paranoia into an art form. It's time to level up your crypto survival skills.
