Belt - REKT

Welcome to the slaughterhouse.
An incorrect share valuation helps to add another notch to the now infamous flash loan exploit season on the BSC.
Yet another fork of a fork has rolled off the conveyor belt with $6.3M falling straight into the hands of the hacker.
Despite this being a slightly more sophisticated attack than some of the previous occurrences, all the familiar hallmarks are present.
Another BSC protocol caught with its trousers down.
Why do these projects continue to leave themselves vulnerable to such savage beatings?
With the bull market seeming to stall, is it time for hackers to take profit?

1: Use 8 flash loans on $385M BUSD from PancakeSwap
2: Deposit 10M BUSD in bEllipsisBUSD strategy (only for the first transaction, where it was the 'Most Undersubscribed Strategy')
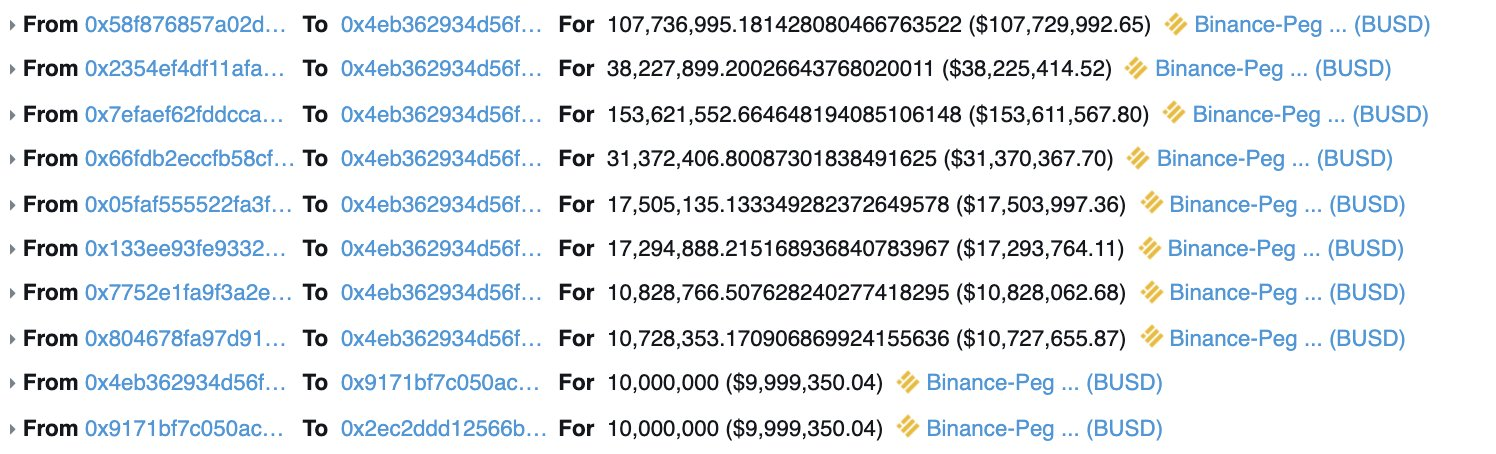
3: Deposit 187M BUSD to bVenusBUSD strategy ('Most Undersubscribed Strategy')
4: Swap 190M BUSD to 169M USDT through Ellipsis
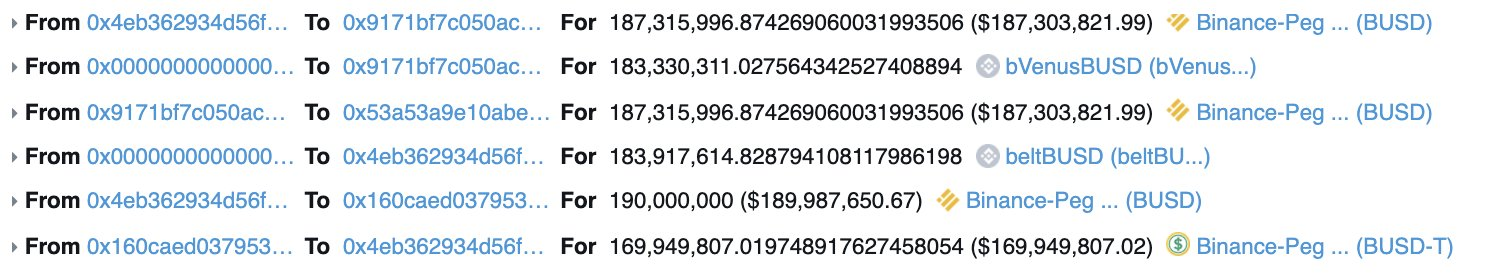
5: Withdraw more BUSD from bVenusBUSD strategy ('Most Oversubscribed Strategy')
6: Swap 169M USDT to 189M BUSD through Ellipsis
7: Deposit BUSD to bVenusBUSD strategy ('Most Undersubscribed Strategy')
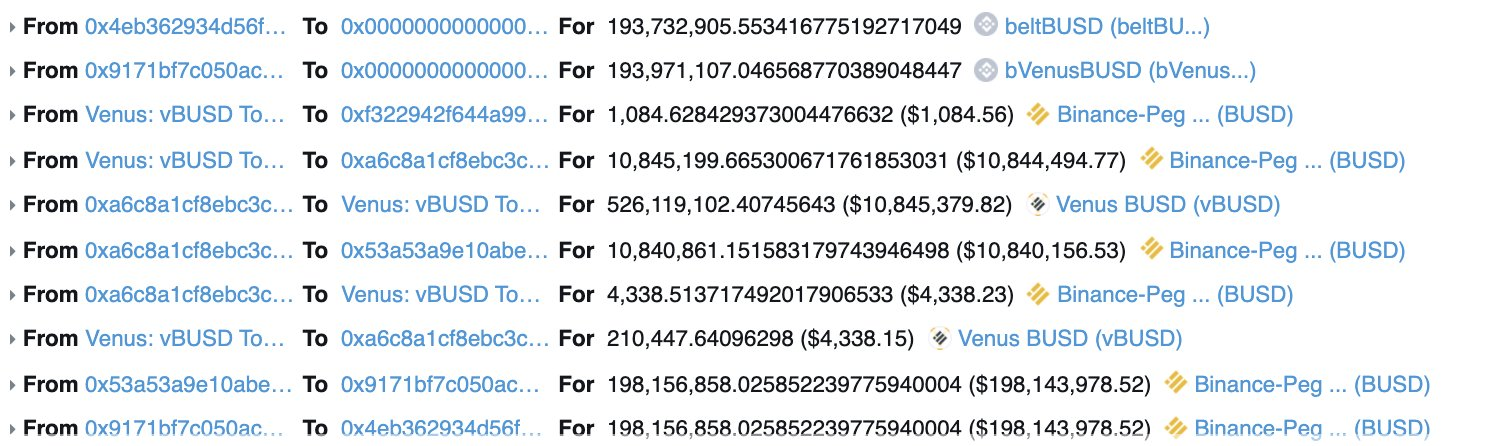
(Steps 4 - 7 were repeated 7 times)
8: Repay flash loans and withdraw profit
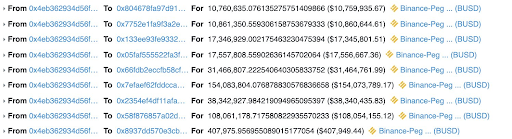
The hacker was not the only one to profit, as the EPS LP and stakers also received their share of this incident.
Credit: FrankResearcher and Mudit__Gupta

The similarities between this exploit and the Harvest Finance hack which we covered in October have not gone unnoticed.
A startlingly familiar series of events led to the Harvest Hacker getting away with over $25m in stolen funds on that occasion and look who was boasting about their new collaboration just two days before this latest incident.
Could the attack come from an external project on the seemingly clueless developers at Belt?

With Binance loosely weighing in on the situation, it seems there is no end in sight for the BSC bloodbath.
Which BSC protocol will be the next to buckle under pressure?

REKT serves as a public platform for anonymous authors, we take no responsibility for the views or content hosted on REKT.
donate (ETH / ERC20): 0x3C5c2F4bCeC51a36494682f91Dbc6cA7c63B514C
disclaimer:
REKT is not responsible or liable in any manner for any Content posted on our Website or in connection with our Services, whether posted or caused by ANON Author of our Website, or by REKT. Although we provide rules for Anon Author conduct and postings, we do not control and are not responsible for what Anon Author post, transmit or share on our Website or Services, and are not responsible for any offensive, inappropriate, obscene, unlawful or otherwise objectionable content you may encounter on our Website or Services. REKT is not responsible for the conduct, whether online or offline, of any user of our Website or Services.
you might also like...
Lucky Star Currency, FSL - REKT
While SBF's trial occupies the attention of the crypto hivemind, it's business as usual on BSC. $2.79M has been rugged already this week across two shitcoin projects. Who’s still apeing into this stuff?
DeFiLabs - REKT
Yesterday, DeFiLabs rugged $1.6M from its users on BSC via a backdoor function in their staking contract. Random projects rugging on BSC is nothing new. The shitcoin casino claims another set of victims.
Midas Capital - REKT 2
Midas can’t keep hold of their gold. On Saturday they lost $600k to a known vulnerability, again. Weaknesses, once discovered, instantly propagate through the ecosystem… When will they learn?
