Atlantis Loans - REKT
UPDATE: Almost a week after the initial exploit, further funds have been drained, bringing the total lost to $2.5M (as noted by Peckshield).
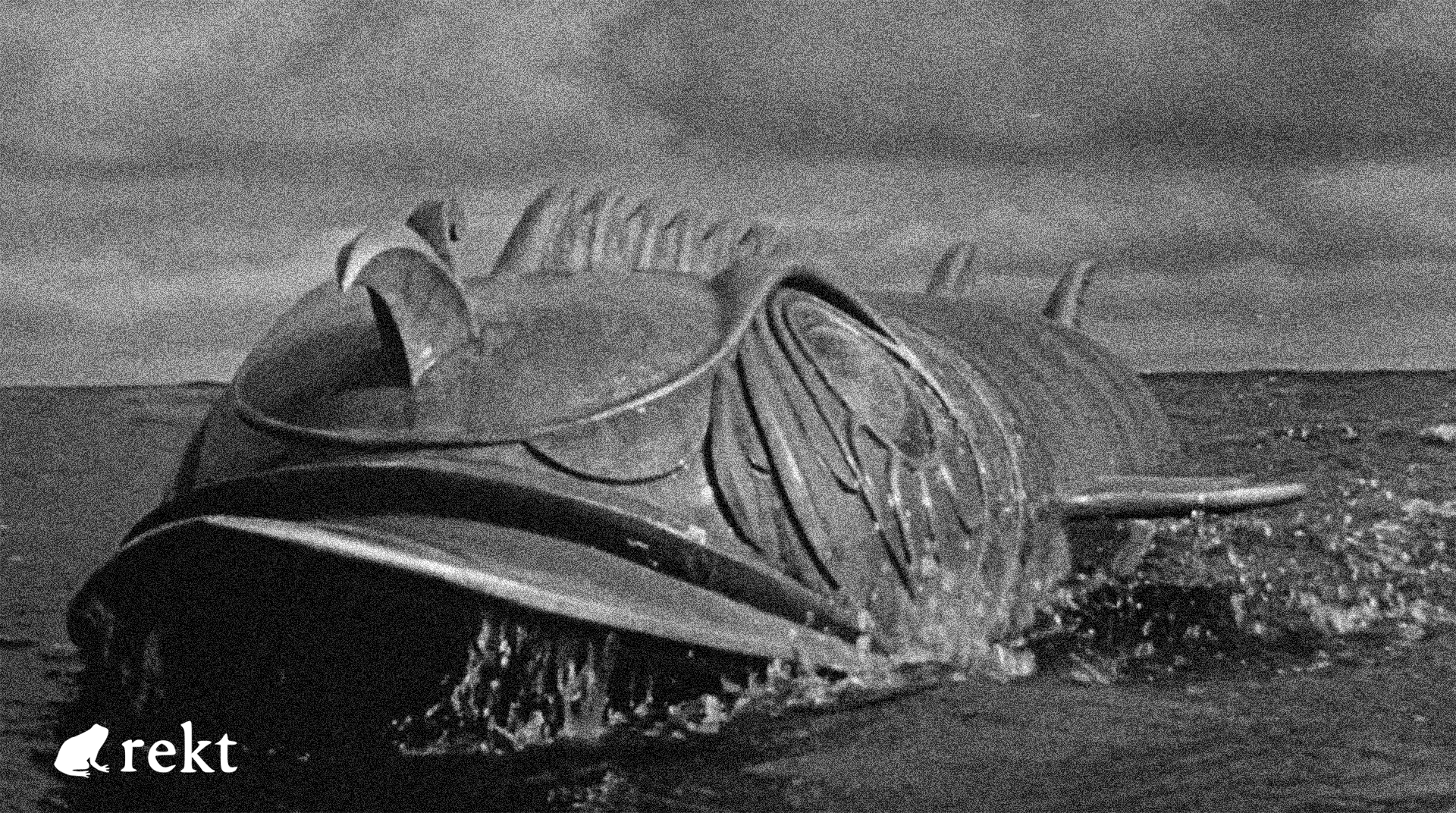
The lost city sunk long ago.
Now, former users have been drained, for a total of ~$1M.
Atlantis Loans was a lending protocol on BSC, before being abandoned by the developers in early April.
Users were informed via a Medium post in which the dev team said they couldn’t afford to continue maintaining the platform. They added:
we believe that discontinuing our services is in the best interest of our users and the protection of their funds.
However, the protocol remained live, with the UI even paid up in advance for two years. As stated in the post:
the only way to make changes or turn things off will have to be done through the governance.
Foreshadowing?

Credit: Beosin, Numen Cyber
The attack had been attempted on the 12th of April, but it failed to pass. With the project abandoned, little attention was paid to the recent proposal 52 published on the 7th June.
The attacker pushed and voted through a governance proposal granting them control of Atlantis Loans’ token contracts. They then upgraded with their own malicious contracts, allowing them to transfer tokens from any address which still had active approvals to Atlantis contracts.
For a full breakdown of how the proposal was executed, see Numen Cyber’s thread.
Full list of contracts to revoke approvals.
Attacker’s address: 0xEADe071FF23bceF312deC938eCE29f7da62CF45b
The attacker was initially funded by Binance on ETH.

Governance attacks can be varied in their scope and effects.
Last month, we saw Tornado Cash’s governance system hijacked by an attacker who snuck code into what was supposed to be a safe proposal.
Last year, Beanstalk got rekt for $181M from a flash loan-enabled governance attack made possible by a lack of execution delay on the proposal.
And in March, Swerve, an also-abandoned Curve-clone, was (unsucessfully) targeted via governance. The proposal would have transferred $1.3M remaining in the DAI-USDC-USDT liquidity pool to the attacker’s address, but they were unable to gather enough tokens to force the vote through.
This week’s case serves not just as a reminder to revoke old token approvals, but highlights the importance of carefully monitoring governance processes, even on defunct projects.
For Atlantis, it looks like it’s back to the murky depths…
…for good this time.

REKT serves as a public platform for anonymous authors, we take no responsibility for the views or content hosted on REKT.
donate (ETH / ERC20): 0x3C5c2F4bCeC51a36494682f91Dbc6cA7c63B514C
disclaimer:
REKT is not responsible or liable in any manner for any Content posted on our Website or in connection with our Services, whether posted or caused by ANON Author of our Website, or by REKT. Although we provide rules for Anon Author conduct and postings, we do not control and are not responsible for what Anon Author post, transmit or share on our Website or Services, and are not responsible for any offensive, inappropriate, obscene, unlawful or otherwise objectionable content you may encounter on our Website or Services. REKT is not responsible for the conduct, whether online or offline, of any user of our Website or Services.
you might also like...
Lucky Star Currency, FSL - REKT
While SBF's trial occupies the attention of the crypto hivemind, it's business as usual on BSC. $2.79M has been rugged already this week across two shitcoin projects. Who’s still apeing into this stuff?
DeFiLabs - REKT
Yesterday, DeFiLabs rugged $1.6M from its users on BSC via a backdoor function in their staking contract. Random projects rugging on BSC is nothing new. The shitcoin casino claims another set of victims.
Midas Capital - REKT 2
Midas can’t keep hold of their gold. On Saturday they lost $600k to a known vulnerability, again. Weaknesses, once discovered, instantly propagate through the ecosystem… When will they learn?
