8ight Finance - REKT
8ight Finance users are out of pocket.
Although this is our first story taking place on the Harmony chain, there’s nothing new about the protocol.
Another Olympus fork, another set of “compromised keys”.
$1.75 million taken.

From the 8ight tweet.
First transaction: 490,170 DAI 0x62f7...
Second transaction: 378,417 DAI - 10,843 LP 0x06f43...
Third transaction: 12,362 USDT 0x0e351...
Transfer from xxca1d account to cc541: 868,587 DAI 0x3880f...
And then to Tornado.

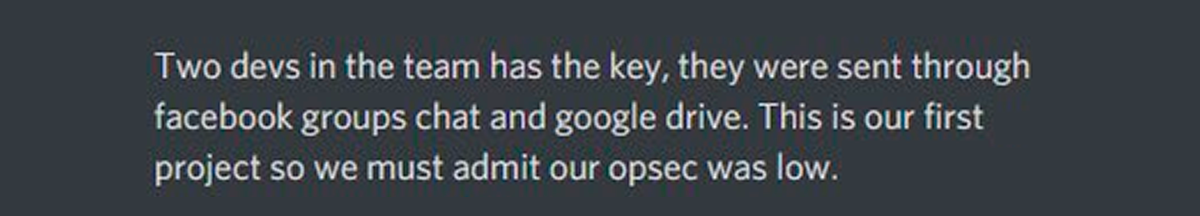
You would hope that we wouldn’t have to say this by now, however…
Don’t post your private keys on Facebook.
Don’t post your private keys in a Google Doc.
Poor OPSEC makes poor users.

”Security 101 - repeat after me…”
Despite their promises that a multi-sig was in place, (it was not), this protocol fell to the most basic of errors.
So basic in fact, that many are accusing the developer of pocketing the funds themselves.
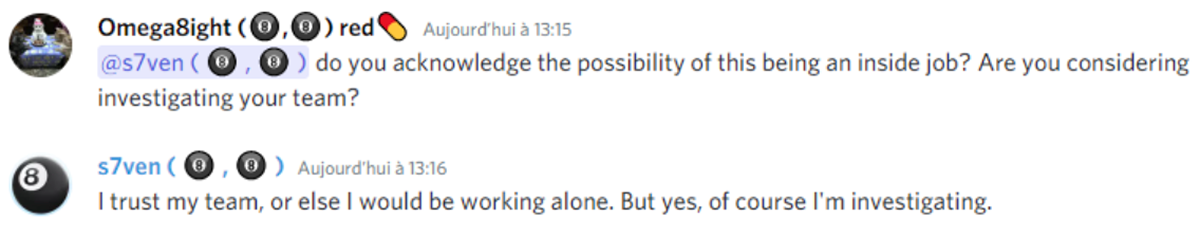
As always, some of the more financially, or emotionally, involved users, are planning their revenge. Have any of these groups of victims ever caught their attacker?
If this was a planned event, then it’s likely that the developers have a history of such behaviour.
But surely they wouldn’t use the same brand name twice?
Would they?

$1.75 million gone, and perhaps the most interesting part of the story is that the developers were still using Facebook.
When will we stop referring to a blatant disregard for cyber security as “getting hacked"?
8ight Finance - maybe hacked, maybe rugged, definitely rekt.

REKT serves as a public platform for anonymous authors, we take no responsibility for the views or content hosted on REKT.
donate (ETH / ERC20): 0x3C5c2F4bCeC51a36494682f91Dbc6cA7c63B514C
disclaimer:
REKT is not responsible or liable in any manner for any Content posted on our Website or in connection with our Services, whether posted or caused by ANON Author of our Website, or by REKT. Although we provide rules for Anon Author conduct and postings, we do not control and are not responsible for what Anon Author post, transmit or share on our Website or Services, and are not responsible for any offensive, inappropriate, obscene, unlawful or otherwise objectionable content you may encounter on our Website or Services. REKT is not responsible for the conduct, whether online or offline, of any user of our Website or Services.
